Effective file management is essential for guaranteeing a productive and organized workspace. Implementing best practices can significantly improve your workflow and minimize the risk of data loss or corruption.
Here are some key guidelines to consider:
* Establish a clear and consistent file naming convention.
* {Regularlybackup your important files.
* Categorize your files into logical folders.
* Leverage version control to track changes.
By following these best practices, you can streamline your file management processes and strengthen overall data security.
Mastering Your Digital Files for Success
In today's online age, we generate a massive amount of data. From messages to papers, keeping track of it all can quickly become a challenging task. Fortunately, with some strategy, you can seamlessly organize your digital files and boost productivity. A well-structured method allows for instant file retrieval, reduces clutter, and promotes a more focused workflow.
Consider these steps to optimize your digital file organization:
- Utilize a clear labeling system.
- Set up dedicated directories for different types of files.
- Continuously archive your critical files to an separate drive.
With implementing these techniques, you can achieve a well-organized digital environment that facilitates your projects.
Understanding File Types and Extensions
Every file on your machine has a unique code called an extension. This little string of characters usually comes after a period (.), and it tells you the type of file it is. For example, a file named "document.docx" is a Word document, while "image.jpg" is a photograph.
Understanding these codes can be beneficial because it enables you to view files correctly and prevent potential problems.
Here's a brief list of common file extensions:
* .docx - Word document
* .pdf - Portable Document Format
* .jpg, .jpeg - Image
* .png - Portable Network Graphics
* .mp3 - Audio file
* .avi, .mp4 - Video file
Learning about different file types and their extensions can enhance your online knowledge.
Protecting Confidential Data: Encryption and Permissions
In today's digital landscape, safeguarding/protecting/preserving sensitive files has become paramount. With the ever-present risk of data breaches and unauthorized access, implementing robust security measures is essential. Two key strategies for securing sensitive information are encryption and access control. Encryption involves transforming data/information/content into an unreadable format, rendering it incomprehensible to anyone without the proper decryption key. This prevents/hinders/obstructs unauthorized parties from accessing and misusing/exploiting/tampering more info with valuable data.
- Furthermore/Additionally/Moreover, access control mechanisms define who can view/access/retrieve specific files or systems. This involves implementing user accounts, passwords, and permissions/privileges/authorizations to restrict access based on roles and responsibilities. By combining encryption and access control, organizations can establish a multi-layered security framework that effectively protects/defends/safeguards sensitive information from unauthorized disclosure.
Troubleshooting Common File Issues
When dealing with files, you may encounter various difficulties that can disrupt your workflow. These failures can range from simple file corruption to more complex system-level problems.
One common issue is a file being unreadable. This can occur if the file has been damaged, deleted unexpectedly, or if there are permissions issues preventing you from accessing it. Another frequent problem is a file being oversized. This can lead to storage space limitations or prevent certain applications from processing the file.
To effectively troubleshoot these common file issues, it's essential to recognize the specific problem you're facing. Then, you can apply appropriate solutions based on the nature of the issue. Some general troubleshooting steps include:
* Inspecting file permissions and ensuring you have the necessary access rights.
* Analyzing files for malware or viruses that may be causing corruption.
* Running a file repair tool to fix corrupted data.
* Minimizing the size of large files if possible.
* Reaching out technical support for more complex issues.
By following these steps and utilizing the appropriate resources, you can effectively resolve common file issues and keep your workflow running smoothly.
Transformation of File Storage Solutions
From the primitive days of punch cards, file storage has undergone a remarkable evolution. What once demanded massive devices and sophisticated systems can now be achieved with compact solutions that blend seamlessly into our digital lives. The ongoing need for optimized storage has led to revolutionary technologies such as network attached storage, each offering its own unique advantages.
This advancement shows no signs of slowing down, with the horizon holding even transformative possibilities for how we preserve our essential data.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now! Kel Mitchell Then & Now!
Kel Mitchell Then & Now! Christina Ricci Then & Now!
Christina Ricci Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now!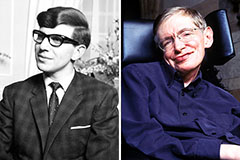 Stephen Hawking Then & Now!
Stephen Hawking Then & Now!